Cisco Vpn 3002
Cisco VPN 3000 Series Concentrators VPN 3005 Concentrator and VPN 3002 Hardware Client Battery Upgrade Instructions with China RoHS Table. Hierarchical Navigation. Step 6 Confirm that the VPN 3005/3002 recognizes the new admin password after the power cycle. Choose Configuration VPN General GroupPolicy. Choose the GroupPolicy you use for your 3002 clients and click Edit. Choose Client Configuration Cisco Client Parameters Store Password on Client System, and then choose the radio button in order to enable it.
Table Of Contents
Introduction
References
Document Organization
Cisco VPN 3002 Hardware Client
Overview
VPN 3002 Interfaces
Roles and Services
Authentication Mechanisms
Physical Security
Cryptographic Key Management
Self-Tests
Design Assurance
Mitigation of Other Attacks
Secure Operation
Crypto-Officer Guidance
Services
User Guidance
Tamper Evidence Labels
Non-FIPS Approved Cryptographic Algorithms
Acronyms
Cisco VPN 3002 Hardware Client Security Policy
Introduction
This non-proprietary Cryptographic Module Security Policy describes how the VPN 3002 and 3002 8E Hardware Client (Firmware version FIPS 3.6.7.F) meets the security requirements of FIPS 140-2, and how to operate a VPN 3002 using IPSec encryption in secure FIPS 140-2 mode. This policy was prepared as part of the Level 2 FIPS 140-2 validation of the VPN 3002 Hardware Client, referred to in this document as the VPN 3002.
This document may be copied in its entirety and without modification. All copies must include the copyright notice and statements on the last page.
FIPS 140-2 (Federal Information Processing Standards Publication 140-2—Security Requirements for Cryptographic Modules) details the U.S. Government requirements for cryptographic modules. More information about the FIPS 140-2 standard and validation program is available on the NIST website at:
http://csrc.nist.gov/cryptval/
This document contains the following sections:
References
This document describes the operations and capabilities of the VPN 3002 only in the technical terms of FIPS 140-2 cryptographic module security policy. More information is available on the VPN 3002 Hardware Client in the following documents:
VPN 3002 Hardware Client Getting Started, Release 3.6—explains how to unpack and install the VPN 3002 and how to configure the minimal parameters.
VPN 3002 Hardware Client Reference, Release 3.6—explains how to start and use the VPN 3002 Hardware Client Manager and how to configure your device beyond the minimal parameters you set during quick configuration. This guide also explains and defines all functions available in the Administration and Monitoring screens of the VPN 3002 Hardware Client Manager.
VPN 3002 Hardware Client Quick Start card summarizes information for quick configuration.
VPN 3002 Hardware Client Basic Information sticky label summarizes information for installing the VPN 3002 and beginning configuration.
Release Notes for Cisco VPN 3000 Series Concentrator, Releases 3.6 Through 3.6.7
You can find this documentation as well as information on the complete line of products from Cisco Systems at the website http://www.cisco.com.
The NIST Validated Modules website (http://csrc.nist.gov/cryptval/) contains contact information for answers to technical or sales-related questions for the modules.
Document Organization
Cisco Vpn 3002
The Security Policy document is one document in a complete FIPS-2 Submission Package. In addition to this document, the complete submission package contains:
•Vendor Evidence document
•Finite State Machine
•Other supporting documentation as additional references
With the exception of this Non-Proprietary Security Policy, the FIPS 140-2 Validation Documentation is proprietary to Cisco Systems and is releasable only under appropriate non-disclosure agreements. For access to these documents, contact Cisco Systems.
Cisco VPN 3002 Hardware Client
This section presents an overview of the VPN 3002, its interfaces, roles and services, authentication mechanisms, cryptographic key management, design assurance, and mitigation of attacks.
Overview
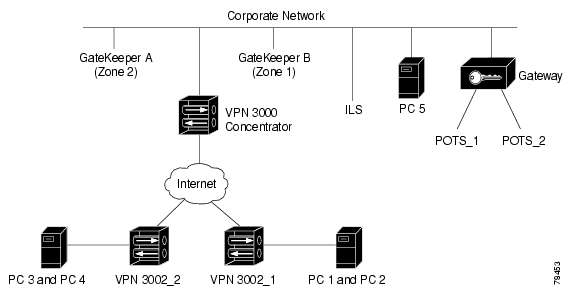
The Cisco VPN 3002 and 3002-8E Hardware Client, referred to in this document as the VPN 3002, is a small hardware appliance that operates as a client in Virtual Private Networking (VPN) environments. It combines the best features of a software client, including scalability and easy deployment, with the stability and independence of a hardware platform. The VPN 3002 connects a remote user to a corporate network. The user connects to a local Internet service provider (ISP), then to the VPN device Internet IP address. The VPN 3002 encrypts the data and encapsulates it into a routable IPSec packet, creating a secure tunnel between the remote user and the corporate network. The corporate server authenticates the user, decrypts and authenticates the IPSec packet, and translates the source address in the packets to an address recognized on the corporate network. This address is used for all traffic sent from the corporate network to the remote user for the duration of the connection. The VPN 3002 distinguishes between tunneled and non-tunneled traffic and, depending on your server configuration, allows simultaneous access to the corporate network and to Internet resources.
VPN 3002 Interfaces
The VPN 3002 is a multi-chip stand-alone module and the cryptographic boundary of the module is defined by its metal enclosure. The module provides a number of physical and logical interfaces to the device.
The physical interfaces that the VPN 3002 provides are mapped to four FIPS 140-2 defined logical interfaces: data input, data output, control input, and status output. The logical interfaces and their module mapping are described in Table 1.
VPN 3002's Physical Interfaces | |
|---|---|
Data input | 10/100BASE-TX LAN ports |
Data output | 10/100BASE-TX LAN ports |
Control input sequence | 10/100BASE-TX LAN ports |
Status output | LEDs |
Power | 3.3 VDC, 4.55 A power inlet |
Roles and Services
VPN 3002 implements role-based authentication. To perform tasks on the VPN 3002, users are required to enter a password and authenticate to the system. Users can access the VPN 3002 in one of the following ways:
•Serial Port
•Hyper Text Transfer Protocol (HTTP)
•HTTPS (over TLS pr SSL)
•Telnet
•Telnet over SSL (Secure Socket Layer)
•SSH
In a FIPS approved mode of operation, only the interfaces through the serial port, HTTPS (using TLS) and SSH (using FIPS-approved algorithms) are enabled.
The VPN 3002 supports three roles by default. These are mapped to the crypto officer and user roles as follows:
FIPS Mapping | |
|---|---|
Admin | Crypto-Officer |
Config and Monitor | Crypto-Officer |
User | User |
Admin Role
The admin is responsible for configuring the VPN 3002 properly, and is considered to be a crypto officer role. The admin can access all the services available via the management interfaces. Descriptions of the services available to the admin role are provided below.
The non-crypto services include show status commands and user establishment and authentication initialization. The non-crypto services available to the admin role include the following:
•Performing general configuration (for example, defining IP addresses, enabling interfaces, enabling network services, and configuring IP routing protocols)
•Reloading and shutting down the VPN 3002
•Displaying full status of the VPN 3002

•Shutting down and restarting network services
•Displaying the configuration file stored in memory, and also the version saved in flash, which is used to initialize the VPN 3002 following a reboot
•Configuring all administrative roles and privileges
•Managing the event log
•Monitoring operations
The crypto services include key generation, encryption/decryption, and the power-up self-tests. The crypto services available to the admin role include:
•Managing certificate enrollment
•Configuring group authentication policy
•Configuring management protocols (public key algorithm, encryption, authentication)
•Configuring filters and access lists for interfaces and users
•Configuring administrator passwords
Admin users may not configure static session keys for encrypted tunnels, nor are they allowed to enter static keys for certificate enrollment. These keys are all generated dynamically via the appropriate mechanism (e.g. IKE negotiations or RSA and DSA digital signatures).
Managing the VPN Concentrator, with which the 3002 Hardware Client is working, is also considered to be a crypto officer role. The VPN 3002 Hardware Client uses the following services from the VPN Concentrator:
•The VPN Concentrator 'pushes' the split tunneling policy to the VPN 3002 over an IPsec tunnel.
•The VPN Concentrators perform the authentication of the VPN 3002 users on behalf of the VPN 3002. If a user tries to login to the VPN 3002, the authentication information is passed onto the VPN Concentrator over the IPSec tunnel, which verifies the information and sends back the status.
The VPN Concentrator and the Hardware Client authenticate to each other using public key certificates during IPSec tunnel negotiation.
Config and Monitor Roles
The VPN 3002 supports two additional administrator roles with restrictive privileges. The administrator roles are also crypto officers but with lesser privileges. These two roles are called `Config' and `Monitor' and are created by default on the module. The admin user can disable them or change their passwords.
For FIPS purposes the administrator role is also considered to be a crypto officer role. The `Config' administrator is a crypto officer with access rights to Quick Configuration and monitoring. The Monitor administrator is a crypto officer with rights to monitoring management options only.
The administrator role is accessed through an Ethernet port using the Web-based administration tool, or by connecting through the console port. All administrator roles are authenticated by the correct username/password combination and passing the appropriate IP address checks.
User Role
Users are the people or entities that wish to send data or traffic through the VPN 3002. Users comprise devices, VPN 3002s, and anyone passing data through the VPN 3002s. All user roles are entered by supplying the correct authentication information. Users are authenticated to the VPN 3002 based on the authentication protocol established by the administrator (for example, security association ID or IP address and preshared secret key combination).
Authentication Mechanisms
The VPN 3002 supports the username-password combination or digital certificates for authenticating users for IPSec tunnel negotiation. To log on to the VPN 3002 for managing the module, an operator (admin) must connect to the VPN 3002 through one of the management interfaces (Serial Port, SSH, HTTP or TLS in FIPS mode) and provide a username and password.
Strength | |
|---|---|
Username-Password mechanism | The module implements a minimum length requirement for the password. The minimum length is six characters. The length of the password makes the probability of getting a random guess correct less that 1 in 1000000. |
Certificate-based authentication | The module supports a public key based authentication. It supports 512, 768 and 1024 bit keys. The signature on each certificate is 128-bits. Thus the probability of getting a random guess correct is much less than 1 in 1000000. This is used to authenticate the client when creating an IPSec tunnel. |
Physical Security
The VPN 3002 Hardware Client is a multi-chip stand-alone cryptographic module.
Cryptographic Key Management
The VPN 3002 uses the following FIPS-approved algorithms.
•Symmetric Key Algorithms
Modes Implemented | ||
|---|---|---|
DES (FIPS 46-3) | CBC | 56 bits |
Triple DES (FIPS 46-3) | CBC | 168 bits |
AES (FIPS 197) | CBC | 128, 196, 256 bits |
•Hashing Algorithm
–SHA-1 (FIPS 180-1)
–HMAC with SHA-1
•Public Key Algorithm
–RSA (PKCS#1)
–DSA (FIPS 186-1)
The VPN 3002 implements the Diffie-Hellman Key exchange algorithm. It also uses the SSL/TLS protocol, SSH protocol and HTTPS for system management.
Cryptographic Keys Used by the VPN 3002
The VPN 3002 uses a variety of keys during its operation. Table 4 lists the keys used by various services and protocols. The VPN 3002 uses PKCS10 format for certificate requests. It also supports the Simple Certificate Enrollment Protocol (SCEP).
Description | Storage and Zeroization | |
Key Encryption Key 1 (KEK1) | An ephemeral triple DES key used to protect all traffic keys, HMAC keys, Diffie-Hellman private keys. KEK1 is used to decrypt the appropriate cryptographic key prior to use. | KEK1 is stored in RAM in plaintext form. It is zeroized by restarting/resetting the module. |
Key Encryption Key 2 (KEK2) | An ephemeral DES key used to protect DSA private keys, RSA private keys, and the Diffie-Hellman shared secret (gxy) private keys. KEK2 is used to decrypt the appropriate cryptographic keys prior to use by the module. | KEK2 is stored in RAM in plaintext form. It is zeroized by restarting/resetting the module. |
RSA public/private keys | Identity certificates for the module itself and also used in IPSec negotiations. | The RSA private key is stored encrypted with KEK2 in the RAM memory. In the Flash they are stored encrypted with a PKCS#5 based encryption mechanism. The pass phrase used for the PKCS#5 encryption is derived from hardware. They are stored in Flash memory and no one can access the Flash to access these keys. |
DSA public/private keys | Identity certificates for the module itself and also used in IPSec negotiations. | The DSA private key is stored encrypted with KEK2 in the RAM memory. In the Flash filesystem they are stored encrypted with a PKCS#5 password based encryption mechanism. The pass phrase used for the PKCS#5 encryption is derived from hardware.They are stored in Flash memory and no one can access the Flash to access these keys. |
Diffie-Hellman Key Pairs | Used by the VPN 3002 devices for key agreementduring the IKE session establishment process. | Diffie-Hellman private keys and shared secrets(gxy) are stored in RAM and protected by encryption using either KEK1 or KEK2. They are zeroized by resetting/rebooting the module. |
Public keys | The VPN 3002 stores public keys of client systems that use the VPN 3002. It also receives the public key of the VPN 3002. | These can be either deleted by the Admin or overwritten with a new value of the certificate from the client. |
TLS Traffic Keys | Used in HTTPS connections to configure the system and also in SSH host keys. | These are ephemeral keys stored in RAM encrypted using KEK1 and are zeroized once the TLS session is closed. |
SSH Host keys and Session Keys | The SSH keys for the VPN module. The keys from clients, from where the operator is connecting are also stored. | The SSH session keys are ephemeral keys stored in RAM encrypted using KEK1. They are zeroized once the SSH session is closed. The SSH host keys are zeroized by either deleting them or by overwriting them with a new value of the key. |
IPSec traffic keys | Exchanged using the IKE protocol and the public/private key pairs. These are DES/3DES or AES keys. | They are ephemeral keys stored in RAM encrypted using KEK1 and are zeroized when the tunnel is closed. |
IKE pre-shared keys | Entered by the crypto officer in plain-text form over the HTTPS(TLS) web interface and are stored in plaintext form. | They are used for authentication during IKE. They are zeoized by |
Password table | Critical security parameters used to authenticate the crypto officer logging in on to the machine. | They are stored in NVRAM and are zeroized by overwriting the password with a new one. |
Group and User passwords | Critical security parameters used to authenticate the Users of the module | They are stored in flash memory using a PKCS#5 derived key. They are zeroized when the passwords are changed. |
Certificates of Certificate Authorities (CAs) | Necessary to verify certificates issued by them. So the CA's certificate should be installed before installing the certificate issued by it. | They are stored in the file system and are signed by the CA to prevent modification. |
Only the crypto officer can log on to the module through an administrative interface (console or web interface). All users access only the services that the VPN 3002 provides. Hence the CSPs stored on the disk are accessed directly only by the crypto officer.
Key Generation
The VPN 3002 uses FIPS-approved random number generators. The VPN 3002 generates all other keys using the pseudo random number generator defined in the ANSI X9.31 standard.
Key Entry and Output
All the keys are entered through the administrative interface. Keys are never output from the VPN 3002.
Key Storage
All cryptographic keys are stored in encrypted form using Key Encryption Keys (KEKs). The only keys that are stored in plain-text form are the KEKs and IPSec pre-shared keys. KEKs are not accessible to anyone and are stored in flash. Also a user thread cannot access shared keys of other users. The passwords are stored in clear text format. The RSA/DSA keys are stored encrypted in the flash using a PKCS#5 based pass-phrase. Keys encrypted with a pass-phrase based PKCS#5 are considered plain text for FIPS purposes.
Key destruction
As required by FIPS 140-2, all keys can be destroyed and the VPN 3002 zeroizes all keys prior to their destruction. Also performing a hardware or software reboot will zeroize all the KEKs and ephemeral session keys.
Self-Tests
The VPN 3002 provides the following power-up self-tests:
•Software/firmware integrity test
•DSA KAT (sign/verify test)
•RSA KAT
•DES KAT
•TDES KAT
•AES KAT
•SHA-1 KAT
•HMAC SHA1 KAT
The VPN 3002 performs all power-up self-tests automatically each time it starts. All power-up self-tests must be passed before allowing any operator to perform any cryptographic services. The power-up self-tests are performed after the cryptographic systems are initialized, but prior to the initialization of the LANs. This prevents the module from passing any data during a power-up self-test failure. In the unlikely event a power-up self-test fails, an event is displayed in the event log indicating the error and then the module logs the error message. In this state, the VPN 3002 does not perform any operations. The operator has to check the logs and cycle the power to attempt to clear the error.
In addition, the VPN 3002 also provides the following conditional self-tests:
•Pair-wise consistency test for DSA key pair generation
•RSA pair wise consistency test for RSA key pair generation
•Continuous Random Number Generator Test for the FIPS-approved RNG
In the unlikely event a conditional self-test fails, an event is displayed in the error log indicating the error and then the module logs the error. In this state the VPN 3002 disables all data output. The operator has to check the logs and cycle the power to attempt to clear the error.
Design Assurance
Cisco Systems uses the Perforce Configuration Management System. Perforce is used in software and document version control, code sharing and build management.
The configuration management system is used for Software Lifecycle Modeling. Software life-cycle modeling is the business of tracking source code as it goes through various stages throughout its life, from development, to testing, release, reuse, and retirement. Cisco Systems also the Perforce Configuration Management system to perform the following processes:
•Workspaces - where developers build, test, and debug
•Codelines - the canonical sets of source files
•Branches - variants of the codeline
•Change propagation - getting changes from one codeline to another
•Builds - turning source files into products
Cisco Systems follows established software engineering principles design, develop, track and document software and hardware modules.
Mitigation of Other Attacks
The VPN 3002 does not claim to mitigate any attacks in a FIPS approved mode of operation.
Secure Operation
The Cisco VPN 3002 meets Level 2 requirements for FIPS 140-2. The sections below describe how to place and keep the module in FIPS-approved mode of operation.
Crypto-Officer Guidance
The following are instructions to the crypto officer to run the module in a FIPS approved mode of operation.
Initial Setup
The following list is a summary of the security rules that the crypto officer must configure and enforce on the VPN 3002s:
•The crypto officer must make sure that the corresponding VPN Concentrator is operating in a FIPS mode.
•Only FIPS-approved cryptographic algorithms to be used.
•Only the IPSec protocol may be enabled for protection of traffic.
•When using HTTPS to protect administrative functions, only the TLS protocol may be used for key derivation. The SSL protocol is not compliant with the FIPS 140-2 standard.
•The crypto officer must change the default password and choose a password that is at least 6 characters long.
•The crypto officer must not perform firmware upgrades in a FIPS mode of operation.
Cryptographic Algorithms
VPN 3002s support many different cryptographic algorithms. However, to properly use VPN 3002s in FIPS mode, only the FIPS-approved algorithms may be used. The following cryptographic algorithms are to be used for encrypting traffic, hashing, or signing/verifying digital signatures:
•DES encryption/decryption
Note For legacy use: Use the DES algorithm only for protecting low sensitivity information. Cisco recommends that you use Triple DES or AES to protect highly sensitive information.
•Triple DES encryption/decryption
•SHA-1 hashing
•DSA signing and verifying
•RSA digital signature signing and verifying
Administrators must configure VPN 3002s to use only the cryptographic algorithms listed above for all services that they provide.
Security Relevant Data Items
VPN 3002s store many security relevant data items, such as authentication keys (Pre-shared keys, DSA or RSA private keys) and traffic encryption keys. All security data items are stored and protected within the VPN 3002 tamper evident enclosure (see section 'Tamper Evidence' for details on applying tamper evident labels). In addition, most security data items are stored encrypted on VPN 3002s.
Services
To operate in FIPS mode, the crypto officer must configure the VPN 3002 as follows:
•Enable HTTPS only. Disable HTTP for performing system management.
•Configure SSL to use only FIPS-compliant encryption algorithms (DES, 3DES, or SHA-1) and set SSL version to TLS V1.
•Configure the Event subsystem to avoid sending events to the console.
•Disable Telnet server.
•Ensure that installed digital certificates are signed using FIPS-compliant algorithms (SHA-1).
•Configure SSH to use only the FIPS-approved encryption algorithms.
•Firmware upgrades are not to be performed in a FIPS mode of operation
User Guidance
The user has to choose a password responsibly and should safeguard it properly without disclosing it.
Tamper Evidence Labels
The VPN 3002 protects all critical security parameters through the use of tamper evident labels. The administrator is responsible for properly placing all tamper evident labels. The security labels recommended for FIPS 140-2 compliance are provided in the FIPS Kit (CVPN3000FIPS/KIT), which you can order for any validated model. These security labels are very fragile and cannot be removed without clear signs of damage to the labels.
You can remove the main encasing of the VPN 3002 like the encasing of a personal computer. The VPN 3002's encasing is attached with four screws at the bottom of the device. Apply the serialized tamper-evidence labels as follows:
Step 1 Turn off and unplug the system before cleaning the chassis and applying labels.
Step 2 Clean the chassis of any grease, dirt, or oil before applying the tamper-evident labels. Alcohol-based cleaning pads are recommended for this purpose.
Step 3 Apply two tamper-evident labels one on each side of the box such that the label covers the side of the encasing and the bottom of the box.
Step 4 Record the serial numbers of the labels applied to the system in a security log.
Step 5 A minimum of 12 hours is required for the labels to cure properly before the module can be used in a secure mode of operation.
Non-FIPS Approved Cryptographic Algorithms
The following cryptographic algorithms are not FIPS-compliant algorithms.
Symmetric Key Algorithms
•40- and 128-bit RC4. CBC mode implemented
Hashing Algorithms
•MD5
•HMAC with MD5
Acronyms
ANSI | American National Standards Institute |
|---|---|
CMVP | Cryptographic Module Validation Program |
CSE | Communications Security Establishment |
CSP | Critical Security Parameter |
EDC | Error Detection Code |
EMC | Electromagnetic Compatibility |
EMI | Electromagnetic Interference |
FCC | Federal Communication Commission |
FIPS | Federal Information Processing Standard |
HTTP | Hyper Text Transfer Protocol |
HTTPS | Hyper Text Transfer Protocol over Secure Socket Layer, or HTTP over SSL |
IKE | Internet Key Exchange |
KAT | Known Answer Test |
LED | Light Emitting Diode |
MAC | Message Authentication Code |
NIST | National Institute of Standards and Technology |
NVLAP | National Voluntary Laboratory Accreditation Program |
RAM | Random Access Memory |
RSA | Rivest Shamir and Adleman |
SHA | Secure Hash Algorithm |
SSH | Secure Shell |
SSL | Secure Sockets Layer |
TLS | Transport Layer Security |
Cisco VPN 3002 Hardware Client Security Policy
Copyright © 2003, Cisco Systems, Inc.
All rights reserved.
Note This document may be copied in its entirety and without modification. All copies must include the copyright notice and statements on the this page.
Posted: Fri Apr 30 10:45:58 PDT 2004
All contents are Copyright © 1992--2004 Cisco Systems, Inc. All rights reserved.
Important Notices and Privacy Statement.
Introduction
This document answers frequently asked questions (FAQs) about the Cisco VPN 3000 Series Concentrator.
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
General
Q. What does the error message 'Lost Service' mean?
A. If there is no traffic sent between the VPN Concentrator and the VPN Client for a period of time, a Dead Peer Detection (DPD) packet is sent from the VPN Concentrator to the VPN Client to ensure its peer is still there. If there is a connectivity issue between the two peers where the VPN Client does not respond to the VPN Concentrator, the VPN Concentrator continues to send DPD packets over a period of time. This terminates the tunnel and generates the error if it does not receive a response during that time. Refer to Cisco bug ID CSCdz45586 (Support contract required).
The error should look like this:
Cause: The remote IKE peer did not respond to keepalives within the expected window of time, so the connection to the IKE peer was deleted. The message includes the keep-alive mechanism used. This issue is only reproducible if the public interface is disconnected during an active tunnel session. The customer needs to monitor their network connectivity as these events are generated to pinpoint the root cause of their potential network connectivity issue(s).
Disable IKE keepalive by going to %System Root%Program FilesCisco SystemsVPN ClientProfiles on the Client PC that experiences the issue, and edit the PCF file (where applicable) for the connection.
Change the 'ForceKeepAlives=0' (default) to 'ForceKeepAlives=1'.
If the problem persists, open a Service Request with Cisco Technical Support and provide the Client 'Log Viewer' and the VPN Concentrator logs as the problem occurs.
Q. What does the error message 'q_send' failures detected for EMQ1 queue mean?
A. This error message occurs when there are too many debug events / information in the buffer. It has no negative impact other than possibly losing a few event messages. Try to reduce the events to the minimum number needed to prevent the message.
Q. My deleted group still shows in the VPN Concentrator configuration. How do I delete this?
A. Copy the configuration into a text editor (such as Notepad) and manually edit or delete the affected group information denoted by [ipaddrgrouppool #.0]. Save the configuration and upload it to the VPN Concentrator. An example is shown here.
Q. Is it possible to have multiple primary SDI servers?
A. The VPN 3000 Concentrators are only able to download one node secret file at a time. In SDI Version pre-5.0, you can add multiple SDI servers, but they must all share the same node secret file (think of it as the primary and backup servers). In SDI Version 5.0, you are only able to enter the one primary SDI server (the backup servers are listed in the node secret file) and replica servers.
Q. I am getting an 'SSL certificate will expire in 28 days' Issuer error message. What should I do?
A. The message indicates that your Secure Socket Layer (SSL) certificate will expire in 28 days. This certificate is used to browse into the web management via HTTPS. You can leave the certificate with the default settings, or you can configure different options before you generate the new certificate. Select Configuration > System > Management Protocols > SSL to do this. Select Administration > Certificate Management and click Generate to renew the certificate.
If you are concerned about security on your VPN Concentrator and would like to prevent unauthorized access, disable HTTP and / or HTTPS on the public interface by going to Configuration > Policy Management > Traffic Management > Filters. If you need to get to your VPN Concentrator over the Internet via HTTP or HTTPS, then you can specify access based on source address by going to Administration > Access Rights > Access Control List. You can use the help menu on the top right corner of the window to get more information.
Q. How can I view the user information in the internal user database? It is not visible when I look in the config file.
A. Select Administration > Access Rights > Access Settings, choose Config File Encryption=None, and save the config to view users and passwords. You should be able to search for the specific user.
Q. How many users can the internal database store?
A. The number of users is version-dependent and specified in the Configuration > User Management section of the User Guide for your VPN 3000 Concentrator release. A total of 100 users or groups (the sum of users and groups must equal 100 or less) is possible in VPN 3000 Releases 2.2 through 2.5.2. In VPN 3000 Releases 3.0 and later, the number for the 3005 and 3015 Concentrators remains at 100. For the VPN 3030 and 3020 Concentrator, the number is 500, for the VPN 3060 or 3080 Concentrators, the number is 1000. Also, using an external authentication server improves scalability and manageability.
Q. What is the difference between the tunnel default gateway and the default gateway?
A. The VPN 3000 Concentrator uses the tunnel default gateway to route the tunneled users within the private network (usually the inside router). The VPN Concentrator uses the default gateway to route packets to the Internet (usually the outside router).
Q. If I place my VPN 3000 Concentrator behind a firewall or router running access control lists, which ports and protocols do I need to allow through?
A. This chart lists ports and protocols.
| Service | Protocol Number | Source Port | Destination Port |
|---|---|---|---|
| PPTP Control Connection | 6 (TCP) | 1023 | 1723 |
| PPTP Tunnel Encapsulation | 47 (GRE) | N/A | N/A |
| ISAKMP/IPSec Key Management | 17 (UDP) | 500 | 500 |
| IPSec Tunnel Encapsulation | 50 (ESP) | N/A | N/A |
| IPSec NAT Transparency | 17 (UDP) | 10000 (default) | 10000 (default) |
Note: The Network Address Translation (NAT) Transparency port is configurable to any value in the 4001 through 49151 range. In versions 3.5 or later, you can configure IPsec over TCP by going to Configuration > System > Tunneling Protocols > IPSec > IPSec over TCP. You can enter up to 10 comma-separated TCP ports (1 - 65535). If this option is configured, make sure that these ports are allowed in your firewall or router running access-control lists.
Q. How can I set the VPN Concentrator back to factory defaults?
A. From the File Management screen, delete the 'config' file and reboot. If this file is deleted accidentally, a backup copy, 'config.bak' is kept.
Q. Can I use TACACS+ for Administrative authentication? What should I keep in mind while I do it?
A. Yes, starting in VPN 3000 Concentrator Release 3.0, you can use a TACACS+ for Administrative authentication. After you configure TACACS+, make sure you test authentication before you log out. Improper configuration of TACACS+ can lock you out. This requires a console port login in order to disable TACACS+ and rectify the problem.
Q. What do I do when the administrative password is forgotten?
A. In versions 2.5.1 and later, connect a PC to the console port of the VPN Concentrator using a straight-through RS-232 serial cable with the PC set for:
9600 bits per second
8 data bits
no parity
1 stop bit
hardware flow control on
VT100 emulation
Reboot the VPN Concentrator. After the diagnostic check is complete, a line of three dots (...) appears on the console. Press CTRL-C within three seconds after these dots appear. A menu displays that lets you reset the system passwords to their defaults.
Q. What is the purpose of the group name and group password?
A. The group name and group password are used to create a hash which is then used to create a security association.
Q. Does the VPN Concentrator proxy ARP on behalf of tunneled users?
A. Yes.
Q. Where do I place the VPN 3000 Concentrator in regard to my network firewall?
A. The VPN 3000 Concentrator can be placed in front of, behind, parallel to, or in the demilitarized zone (DMZ) of a firewall. It is not advisable to have the public and private interfaces in the same virtual LAN (VLAN).
Q. Is there any way to disable proxy ARP on the Cisco VPN 3000 Concentrator?
A. Proxy Address Resolution Protocol (ARP) cannot be disabled on the Cisco VPN 3000 Concentrator.
Q. Where can I find bugs filed against the VPN 3000 Concentrator?
A. Users can use the Bug Search Tool (Support contract required) to find detailed information about bugs.
Q. Where can I find configuration examples for the VPN 3000 Concentrator?
A. In addition to the VPN 3000 Concentrator documentation, more configuration examples can be found on the Cisco VPN 3000 Series Concentrator Support Page.
Q. How can I increase the logging to get better debugs for specific events?
A. You can go to Configuration > System > Events > Classes and configure the specific events (such as IPsec or PPTP) to get better debugs. Debugging should only be turned on for the duration of the troubleshooting exercise because it can cause performance degradation. For IPsec debug, turn on IKE, IKEDBG, IPSEC, IPSECDBG, AUTH, and AUTHDBG. If using certificates, then add the CERT class to the list.
Q. How can I monitor the traffic to the VPN 3000 Concentrator?
A. The HTML interface that comes with the VPN 3000 Concentrator allows you to have basic monitoring functionality if you look under Monitoring > Sessions. The VPN 3000 Concentrator can also be monitored through Simple Network Management Protocol (SNMP) using an SNMP manager of your choice. Alternatively, you can purchase the Cisco VPN / Security Management Solution (VMS). The Cisco VMS provides key functionality to assist you if you deploy the VPN 3000 Concentrator Series and require in-depth monitoring of remote access and site-to-site VPNs, based upon IPsec, L2TP, and PPTP. Refer to the VPN Security Management Solution for more details about VMS.
Q. Does the Cisco VPN 3000 Concentrator Series have an integrated firewall? If so, what features are supported?
A. While the series has integrated stateless port / filtering capabilities and NAT, Cisco suggests you use a device like the Cisco Secure PIX Firewall for the corporate firewall.
Q. What routing options and VPN protocols are supported by the Cisco VPN 3000 Concentrator Series?
A. The series supports these routing options:
Cisco Vpn 3002 Hardware Client
Routing Information Protocol (RIP)
RIP2
Open Shortest Path First (OSPF)
static routes
Virtual Router Redundancy Protocol (VRRP)
Supported VPN protocols include Point-to-Point Tunneling Protocol (PPTP), L2TP, L2TP / IPsec, and IPsec with or without a NAT device between the VPN 3000 and the end client. IPsec through NAT is known as NAT Transparency.
Q. What authentication mechanisms / systems does the Cisco VPN 3000 Concentrator Series support for client PCs?
A. NT Domain, RADIUS or RADIUS proxy, RSA Security SecurID (SDI), Digital Certificates, and internal authentication are supported.
Q. Can I do static Network Address Translation (NAT) for users going out through the VPN 3000 Concentrator?
A. You can only do Port Address Translation (PAT) for the users going out. You cannot do static NAT on the VPN 3000 Concentrator.
Q. How can I assign a static IP address to a specific Point-to-Point Tunneling Protocol (PPTP) or IPsec user through the VPN 3000 Concentrator?
A. This list explains how to assign static IP addresses:
PPTP users
In the IP Address Management section, in addition to choosing your pool or Dynamic Host Configuration Protocol (DHCP) options, check the Use Client Address option. Then, define the user and the IP address in the VPN 3000 Concentrator. This user always get the IP address configured in the VPN Concentrator when connecting.
IPsec users
In the IP Address Management section, in addition to choosing to your pool or DHCP options, check the Use Address from Authentication Server option. Then, define the user and the IP address in the VPN 3000 Concentrator. This user always gets the IP address configured in the VPN Concentrator when connecting. All others that belong to the same group or to other groups gets an IP address from the global pool or DHCP.
With the Cisco VPN 3000 Concentrator software version 3.0 and later, you have the option to configure an address pool on a group basis. This feature can help you to assign a static IP address to a specific user as well. If you configure a pool for a group, the user with static IP gets the IP address assigned to them, and other members of the same group get IP addresses from the group pool. This only applies when you use the VPN Concentrator as an authentication server.
Note: If you use an external authentication server, then you need to use the external server to assign the addresses correctly.
Q. What are some known compatibility issues with Microsoft's PPTP products and the VPN 3000 Concentrator?
A. This information is based on VPN 3000 Series Concentrator Software Release 3.5 and later; VPN 3000 Series Concentrators, Models 3005, 3015, 3020, 3030, 3060, 3080; and Microsoft Operating Systems Windows 95 and later.
Windows 95 Dial-Up Networking (DUN) 1.2
Microsoft Point-to-Point Encryption (MPPE) is not supported under DUN 1.2. To connect using MPPE, install Windows 95 DUN 1.3. You can download the Microsoft DUN 1.3 upgrade from the Microsoft web site.
Windows NT 4.0
Windows NT is fully supported for Point-to-Point Tunneling Protocol (PPTP) connections to the VPN Concentrator. Service Pack 3 (SP3) or later is required. If you are running SP3, you should install the PPTP Performance and Security patches. Refer to the Microsoft web site for information about the Microsoft PPTP Performance and Security Upgrade for WinNT 4.0 .
Note that the 128-bit Service Pack 5 does not handle MPPE keys correctly, and PPTP can fail to pass data. When this occurs, the event log shows this message:
To solve this problem, download the upgrade for How to obtain the latest Windows NT Service Pack 6a and Windows NT 4.0 Service Pack 6a Available. Refer to the Microsoft article MPPE Keys Not Handled Correctly for a 128-Bit MS-CHAP Request for more information.
Cisco Vpn 3002 Hardware Client
Q. What is the maximum number of filters allowed on a VPN 3000 Concentrator?
A. The maximum number of filters that you can add on a VPN 30xx unit (even a 3030 or 3060) is fixed at 100. Users can find additional information about this issue by viewing Cisco bug ID CSCdw86558 (Support contract required).
Q. What is the maximum number of routes in the 30xx line of VPN Concentrators?
A. The maximum number of routes are:
The VPN 3005 Concentrator previously held a maximum of 200 routes. This number has now increased to 350 routes. Refer to Cisco bug ID CSCeb35779 (Support contract required) for more details.
The VPN 3030 Concentrator has been tested up to 10,000 routes.
The routing table limit on the VPN 3030, 3060, and 3080 Concentrators is proportional to the available resources / memory in each device.
The VPN 3015 Concentrator has no predefined maximum limit. This holds true for Routing Information Protocol (RIP) and Open Shortest Path First (OSPF) protocol.
The VPN 3020 Concentrator - Due to a Microsoft limitation, Windows XP PCs are not capable of receiving a large number of Classless Static Routes (CSR). The VPN 3000 Concentrator limits the number of CSRs that are inserted into a DHCP INFORM message response when configured to do so. The VPN 3000 Concentrator limits the number of routes to 28-42, depending on the class.
Q. How do I completely clear the interface statistics on the VPN 3000 Concentrator?
A. Select Monitoring > Statistics > MIB-II > Ethernet and reset the statistics to clear statistics for the current session. Remember that this does not totally clear the statistics. You need to reboot to actually reset the statistics (versus resetting for monitoring purposes).
Q. What ports should I allow on the VPN Concentrator for Network Time Protocol (NTP) communication?
A. Allow TCP and UDP port 123.
Q. What are the functions of UDP ports 625xx?
A. The ports are used for the VPN Client communication between the actual shim / Deterministic NDIS Extender (DNE) and the TCP / IP stack of the PC, and are for internal developmental use only. For example, port 62515 is used by the VPN Client for sending information to the VPN Client log. Other port functions are shown here.
62514 - Cisco Systems, Inc. VPN Service to Cisco Systems IPsec Driver
62515 - Cisco Systems IPsec Driver to Cisco Systems, Inc. VPN Service
62516 - Cisco Systems, Inc. VPN Service to XAUTH
62517 - XAUTH to Cisco Systems, Inc. VPN Service
62518 - Cisco Systems, Inc. VPN Service to CLI
62519 - CLI to Cisco Systems, Inc VPN Service
62520 - Cisco Systems, Inc. VPN Service to UI
62521 - UI to Cisco Systems, Inc. VPN Service
62522 - Log Messages
62523 - Connection Manager to Cisco Systems, Inc. VPN Service
62524 - PPPTool to Cisco Systems, Inc. VPN Service
Q. Can I remove the WebVPN floating bar?
A. You cannot remove the floating tool bar nor avoid loading the floating toolbar while you establish the WebVPN session. This is because when you close this window the session is terminated immediately and when you try to login again the window is loaded again. This is the way the WebVPN sessions were designed originally. You can close the main window but it is not possible to close the floating window.
Software
Q. Does WebVPN support Outlook Web Access (OWA) 2003?
A. OWA 2003 support for WebVPN on the VPN 3000 Concentrator is now available with version 4.1.7 downloads (Support contract required).
Q. Where can I get the latest software revisions for the VPN 3000 Concentrator?
A. All Cisco VPN 3000 Concentrators ship with the most current code, but users can check the downloads (Support contract required) to see if more current software is available.
Refer to the Cisco VPN 3000 Series Concentrator documentation page for the latest documentation on the VPN 3000 Concentrator.
Q. Do I need a TFTP server to upgrade the VPN 3000 Concentrator? Is there an alternative way to upgrade the box?
A. In addition to using TFTP, you can upgrade the VPN Concentrator by downloading the latest software onto your hard drive. Then, from a browser on the system where the software is located, go to Administration > Software Update and find the downloaded software on your hard drive (just like opening a file). When you find it, select the Upload tab.
Q. What does the 'k9' signify in the latest code names (such as in 'vpn3000-3.0.4.Rel-k9.bin')?
A. The 'k9' designation for the image name has replaced the originally used 3DES designation (for example, vpn3000-2.5.2.F-3des.bin). Thus, the 'k9' now signifies that this is a 3DES image.
Q. Should I use the Data Compression option under the IPsec group for all my users?
A. Data compression increases the memory requirement and CPU utilization for each user session and consequently decreases the overall throughput of the VPN Concentrator. For this reason, Cisco recommends that you enable data compression only if every member of the group is a remote user that connects with a modem. If any member of the group connects through broadband, do not enable data compression for the group. Instead, divide the group into two groups, one for modem users and the other for broadband users. Enable data compression only for the group of modem users.
Other Advanced Features
Q. Does load balancing work with LAN-to-LAN connections?
A. Load balancing is effective only on remote sessions initiated with the Cisco VPN Software Client (Release 3.0 and later). All other clients (PPTP, L2TP) and LAN-to-LAN connections can connect to a VPN Concentrator on which load balancing is enabled, but they cannot participate in load balancing.
Q. How do I decrypt the passwords from the config file?
A. Go to Configuration > System > Management Protocols > XML and then to administration | file management select XML format. Use the same name, or different, and open the file in order to view the passwords.
Q. Can I use Virtual Router Redundancy Protocol (VRRP) and load balancing together?
A. You cannot use load balancing with VRRP. In a VRRP configuration, the backup device remains idle unless the active VPN Concentrator fails. In a load balancing configuration, there are no idle devices.
Q. Does all remote access client VPN traffic have to go through an encrypted tunnel to the VPN Concentrator at the enterprise or service provider? For example, can plain web access to other sites go in the open, directly through the ISP's Internet connection?
A. Yes. This concept is known as 'split tunneling.' Split tunneling allows for secure access to corporate resources through an encrypted tunnel while it allows Internet access directly through the ISP's resources (this eliminates the corporate network from the path for web access). The Cisco VPN 3000 Concentrator Series to both the Cisco VPN Client and the VPN 3002 Hardware Client can support split tunneling. For additional security, this feature is controllable by the administrator of the VPN Concentrator and not the user.
Q. Is it safe to use split tunneling?
A. Split tunneling allows you to have the convenience of browsing the Internet while connected through the VPN tunnel. However, it does pose us some risk if the VPN user connected to the corporate network is vulnerable to attacks. It is recommended that the users use a personal firewall in that case. The release notes for any given VPN Client version discuss interoperability with personal firewalls.
Q. How does load balancing work on the Cisco VPN 3000 Concentrator?
A. Load is calculated as a percentage derived from the active connections divided by the maximum configured connections. The director always tries to have the least load because it is burdened with the additional (inherent) load of maintaining all of the administrative LAN-to-LAN sessions, calculating all other cluster member loading, and it is responsible for all client redirects.
For a newly configured functional cluster, the director has about a 1 percent load before any connections have been established. Therefore, the director redirects connections to the backup concentrator until the percentage of load on the backup is higher than the percentage of load on the director. For example, given two VPN 3030 Concentrators in 'idle' states, the director has a 1 percent load. The secondary is given 30 connections (2 percent load) before the director accepts connections.
In order to verify that the director accepts connections, go to Configuration > System > General > Sessions and lower the maximum number of connections to an artificially low number to quickly increase the load placed on the backup VPN Concentrator.
Q. How many headend devices can the VPN Monitor track?
A. The VPN Monitor can track 20 headend devices. In a hub-and-spoke scenario, connections from remote sites are monitored at the headend. There is no need to monitor all the remote sites and users since that information can be traced on the hub router. These headend devices can support up to 20,000 remote users or 2,500 remote sites. A dual-homed VPN device that goes out to the spoke sites counts as two of the 20 maximum devices that can be monitored.
Related Information
